Tolerisk Bolsters Advisory Board With Renowned Cybersecurity Expert by Tolerisk Brian Edelman joins an esteemed group of 10 industry leaders MARLTON, NEW JERSEY, UNITED STATES, March 19, 2024 /EINPresswire.com/ — Tolerisk, a leading provider…
News
Ian McKenna Shares Advice from FCI CEO & Cybersecurity Expert Brian Edelman
- By FCI -
- March 4, 2024 -
What will it take to scare firms into action? by Ian McKenna Every time I meet Brian Edelman, chief executive of FCI Cyber, I am petrified by what he tells me. But I am…
FCI Mentioned In The 2024 T3 / Information Advisor Software Survey
- By FCI -
- January 25, 2024 -
LAS VEGAS, NV – January 25, 2024 – FCI proudly announces its inclusion in the esteemed 2024 T3 / Information Advisor Software Survey. This acknowledgment highlights FCI’s dedication to delivering exceptional and innovative cybersecurity solutions. …
To Enhance Security and Compliance, FCI Invites Financial Services Vendors to Add Zero Trust MFA Feature to their Software
- By FCI -
- January 22, 2024 -
LAS VEGAS, NV – January 22, 2024: FCI is pleased to announce its alignment with the latest CISA guidance on Phishing-Resistant MFA and the CISA Zero Trust Maturity Model. This strategic move aims to bolster…
FCI Announces Alignment with New NYDFS Cybersecurity Assessment Regulatory Requirements
- By FCI -
- January 22, 2024 -
LAS VEGAS, NV – January 22, 2024: FCI announces the alignment of its Cyber Safeguards and Technical Controls Assessment Services with the latest NYDFS Regulatory Requirements (Second Amendment to 23 NYCRR 500) and upcoming SEC…
EBIX: Guard Yourself Against An Expensive Data Breach
- By FCI -
- October 10, 2023 -
Ebix and FCI’s CEO Brian Edelman hosted a comprehensive webinar that dives deep into cybersecurity and compliance. In this webinar, Tony Wang and Giles Brown also provide valuable tips for cybersecurity professionals. Brian Edelman…
Ebix Hosts Webinar Featuring FCI CEO Brian Edelman
- By FCI -
- September 28, 2023 -
Protect yourself from a costly data breach! Cyberattacks pose a threat to firms, affecting them in various ways. These attacks can result in financial losses, ransom payments, and regulatory fines. Secondly, cyberattacks can damage a…
FCI CEO Brian Edelman, to speak at Wells Fargo FiNet Annual Conference
- By FCI -
- September 27, 2023 -
We are thrilled to announce that Brian Edelman, the esteemed CEO of FCI and a renowned cybersecurity expert, has been invited to speak at the highly anticipated Wells Fargo FiNet Annual Conference event in Grapevine…
SEC Adopts Proposed Cybersecurity Disclosure Rules
- By FCI -
- August 30, 2023 -
As you know, the Securities and Exchange Commission (SEC) has been working on new cybersecurity disclosure rules for over a year. A few days ago, the SEC adopted the new rules on a vote of…
Financial Planning Interviews Cybersecurity Expert Brian Edelman
- By FCI -
- July 5, 2023 -
Why Wealth Managers Should Celebrate Stalemates in the Never-Ending Cybersecurity Battle By Justin Mack New research released by Financial Planning sister publication American Banker and conducted by parent company Arizent finds that banks and…
$37.5 Million Dollars and the SEC’s Continued Focus on Off Channel Communications
- By FCI -
- June 12, 2023 -
In early May 2023, The Securities and Exchange Commission (SEC) announced a large enforcement action against broker dealers HSBC Securities Inc. and Scotia Capital Inc., which ultimately totaled $37.5 million in fines. This was a…
Financial Planning Webinar Features Cybersecurity Expert Brian Edelman, FCI CEO
- By FCI -
- June 6, 2023 -
On June 8, 2023, Financial Planning will offer a cybersecurity webinar “Connected and Protected: The New Age of RIA Cybersecurity” in partnership with Atria Wealth Solutions, featuring Cybersecurity Expert and FCI CEO Brian Edelman. …
FCI CEO & Cybersecurity Expert Brian Edelman to Speak at TradePMR Conference
- By FCI -
- May 30, 2023 -
TradePMR, a technology and custodial services provider for Registered Investment Advisers (RIAs), will host Synergy23 in Tampa, FL, May 31-June 2 where Financial Advisor attendees will experience 3 days of valuable insights and information designed…
FINRA’s Guidance and Insights Concerning Cybersecurity
- By FCI -
- April 7, 2023 -
Earlier this year, the Financial Industry Regulatory Authority (“FINRA”) published its 2023 Report on FINRA’s Examination and Risk Monitoring Program (the “Report”). The Report emphasized that FINRA believes “cybersecurity remains one of the principal operational…
Cybersecurity Expert & FCI CEO, Brian Edelman Offers Guidance for More Secure Retirement Plan Management
- By FCI -
- April 3, 2023 -
“Who is liable when cyber theft occurs?” is a featured question in the Spring 2023 edition of PLANADVISER magazine citing the cybersecurity responsibilities of retirement plan recordkeepers and sponsors to protect participants. The article…
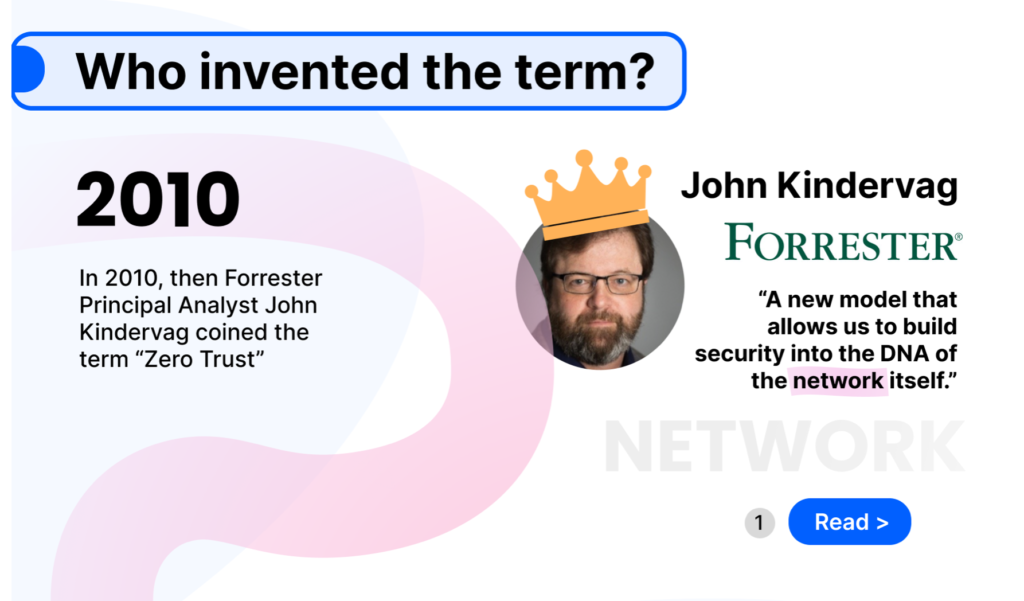
FCI Launches Zero-Trust Complete – The First Truly Integrated Solution that Covers the Four Areas of Zero-Trust Cybersecurity
- By FCI -
- March 28, 2023 -
FCI announces the launch of Zero-Trust Complete, the first genuinely Integrated solution that covers the four areas of Zero-Trust Cybersecurity: Software, Users, Endpoints, and Networks. Brian Edelman, FCI’s Founder and CEO comments, “There’s confusion…
Cybersecurity Expert & FCI CEO, Brian Edelman Presents at T3 Conference
- By FCI -
- March 13, 2023 -
The T3 Conference being held March 13-16, 2023, in Tampa, FL brings together technology vendors, industry leaders, financial advisors and financial services executives from banks, custodians, independent broker/dealers, insurance companies and large RIA networks. …
SEC Rule Nearing Implementation
- By FCI -
- March 7, 2023 -
Although the last few updates have concerned the New York Department of Financial Services (“DFS”) and its proposed amendments to its Cybersecurity Regulation, 23 NYCRR Part 500, it is important to remember that the Securities…
FCI Participates in Ebix Envision 2023
- By FCI -
- February 21, 2023 -
FCI joined the Ebix Envision 2023 User Group & Expo held February 21–23, which brought together Ebix users and solution partners to exchange ideas and explore Ebix’s exciting vision for shaping the industry. FCI…
2023 and DFS Proposed Amendments
- By FCI -
- February 6, 2023 -
As discussed prior, in late 2022 the New York Department of Financial Services (“DFS”) published proposed amendments to its Cybersecurity Regulation, 23 NYCRR Part 500 (“Proposed Amendments”). If the Proposed Amendments are adopted, they would…
Broker World Article Highlights FCI as Cybersecurity Regulatory Compliance Solution
- By FCI -
- February 1, 2023 -
“Beware Of Cybersecurity Risks And How To Implement Regulatory Compliant Solutions” By Ken Leibow Cybersecurity is of critical importance in the financial services industry due to the sensitive nature of the data being handled…
Cybersecurity Expert & FCI CEO Brian Edelman cited in PLANADVISER Article
- By FCI -
- January 11, 2023 -
“Personalization Push Heightens Need for Advisers to Vet Cybersecurity” by Alex Ortolani As the retirement industry moves toward more personalization for participants to plan and save, the chance for bad actors to gain access…
Bob Veres Interviews Brian Edelman, FCI CEO & Cybersecurity Expert, for Inside Information Cybersecurity Special Edition
- By FCI -
- December 11, 2022 -
> Read the Article > Subscribe to Bob Veres’ Inside Information The December 2022 Inside Information edition highlighting “Data Security and Compliance” showcases Brian Edelman’s recommendations of the best ways to protect your…
PLANSPONSOR Article Cites Cybersecurity Expert & FCI CEO, Brian Edelman
- By FCI -
- December 7, 2022 -
“Why Cybersecurity for Retirement Plans is More Important Than Ever” by Alex Ortolani Following Brian Edelman’s CNBC FA Summit “Securing Your Savings” appearance, PLANSPONSOR shared important cybersecurity recommendations to help firms ensure that plan…
The New York Department of Financial Services Cybersecurity Regulation Proposed Amendments
- By FCI -
- December 6, 2022 -
The New York Department of Financial Services (“DFS”) recently released a proposed second amendment to the Cybersecurity Regulation, 23 NYCRR Part 500 (“Proposed Amendments”), which if adopted would go into effect sometime in 2023. The…
FCI CEO & Cybersecurity Expert Brian Edelman Named Featured Speaker at CNBC 2022 Financial Advisor Summit
- By FCI -
- November 21, 2022 -
Brian Edelman will join host Eamon Javers, CNBC Senior Washington Correspondent, as a featured cybersecurity speaker for the 2022 Financial Advisor Summit on Dec 6, 2022. “Securing Your Savings” is a panel discussion that every…
Preserving Attorney Client Privilege For Cybersecurity Vulnerabilities
- By FCI -
- November 1, 2022 -
Firms should be aware of making potential admissions when assessing their cybersecurity risks, including when investigating an actual data breach. There have been a number of cases over the last several years that clearly illustrate…
FCI Sponsored Cybersecurity Panel Discussion
- By FCI -
- October 17, 2022 -
FCI sponsored a cybersecurity panel discussion at the Security, Privacy, Risk & Compliance Retreat, Amelia Island, FL hosted by Sub-Four Capital. The security retreat brought together top C-level executives from Large Enterprises, Mid-Market, SMBs,…
FCI Shares a New Model to Improve Commercial Cyber Insurance Loss Ratios at InsureTech Connect, Las Vegas
- By FCI -
- September 20, 2022 -
Enhanced Pre & Post Breach Cyber Risk Management for a Growing Line of Business InsureTech Connect, Las Vegas, September 20, 2022: FCI, an MSSP focused on Financial Services, is eager to share a new…
Cybersecurity Insurance Developments
- By FCI -
- September 6, 2022 -
The cybersecurity insurance market continues to evolve and there are some important developments for your consideration. In short, although cybersecurity insurance is an important component in your cybersecurity plan (e.g., mitigating costs), it is critical…
FCI article about OCSF in T3 / Technology Tools for Today
- By FCI -
- August 17, 2022 -
T3 published a new article about Coalition Of Cybersecurity Leaders Launch Open Cybersecurity Schema Framework (OCSF) written by FCI. Link to the article: https://t3technologyhub.com/coalition-of-cybersecurity-leaders-launch-open-cybersecurity-schema-framework-ocsf/
FCI Layers Zero Trust Across Four Critical Areas for Greater Compliance
- By FCI -
- July 26, 2022 -
BLOOMFIELD, NJ, July 26, 2022: FCI announced today that is has mapped the four critical areas of Zero Trust including: Users, Endpoints, Software, and Networks that are required for true compliance and overall cybersecurity. Clarifying…
FCI Named Amongst “Top 10 Endpoint Security Companies 2022” by Enterprise Security Magazine
- By FCI -
- July 12, 2022 -
BLOOMFIELD, NJ, July 12, 2022: FCI, a leading provider of cybersecurity solutions in Financial Services, announced today that it has been selected as one of the “Top 10 Endpoint Security Services Companies 2022” by Enterprise…
SEC Proposes New Cybersecurity Rules
- By FCI -
- July 7, 2022 -
As you may remember, earlier this year the Securities and Exchange Commission (SEC) voted to propose cybersecurity rules and amendments related to disclosures, risk management and security incidents for registered investment advisers and registered investment…
FCI CEO Brian Edelman joins The CJK Group & Sub-Four Capital as Cybersecurity Expert Panel Speaker
- By FCI -
- May 26, 2022 -
On May 22-24, 2022, Brian Edelman joined fellow thought leaders at the Lido House, Newport Beach, CA for panel discussions at the eDiscovery & Information Governance Retreat hosted by the CJK Group and the 2022…
Brian Edelman FCI CEO & Cybersecurity Expert Presents to AssetMark Investment Services Advisors
- By FCI -
- May 13, 2022 -
On May 12, 2022, Brian Edelman joined AssetMark to present cybersecurity best practices for data protection and regulatory compliance to its financial advisors. Welcomed by “happy to be in-person again” attendees, Brian presented on the…
CISA Security Alert: Protecting Against Cyber Threats to Managed Service Providers and their Customers
- By FCI -
- May 11, 2022 -
On May 11, 2022, the national Cybersecurity & Infrastructure Security Agency (CISA) issued a security alert warning about the increase in malicious cyber activity targeting Managed Service Providers (MSPs). Threat actors are focusing on…
Forbes cites Brian Edelman, FCI CEO & Cybersecurity Expert
- By FCI -
- May 10, 2022 -
Link to: “15 Ways to Leverage And Supplement AI In Your Cybersecurity Efforts” With more companies moving to permanent remote or hybrid work models, more endpoints are accessing systems of private data without proper…
Brian Edelman, FCI CEO & Cybersecurity Expert, featured in NAIFA’s Advisor Today article
- By FCI -
- May 6, 2022 -
Link to: Heightened Geopolitical Tensions Drive Cybersecurity Alerts for the Life Insurance Industry There are alerts coming across multiple sources from regulatory bodies to industry-specific regulators, government agencies, consulting firms, and more indicating that…
SEC Examinations Division Names Cybersecurity as a 2022 Exam Priority
- By FCI -
- May 4, 2022 -
Recently, the Division of Examinations of the Securities and Exchange Commission (the “SEC”) released its annual list of examination priorities for 2022. The SEC listed five “significant focus areas.” One of the five is entitled “Information…
FCI Expands Co-Managed Cybersecurity Solutions for Cyber-Regulated Organizations
- By FCI -
- April 19, 2022 -
Leadership, IT Teams and MSPs Gain Increased Access & Shared Visibility BLOOMFIELD, N.J. APRIL 19, 2022: FCI is pleased to announce an expanded offering for Enterprises with deeper Co-Managed Cybersecurity capabilities. New realities call…
Financial Planning article cites Brian Edelman, FCI CEO & Cybersecurity Expert
- By FCI -
- April 7, 2022 -
Link to: “What advisory firms should be doing on cybersecurity” By Tobias Salinger Results of Arizent’s latest cybersecurity survey of financial services business leaders revealed that “Wealth Managers have fallen behind other financial firms…
DFS and SEC Warn Financial Entities of Heightened Cybersecurity Risk
- By John J. Cooney -
- April 5, 2022 -
Both the New York State Department of Financial Services (“DFS”) and the Securities and Exchange Commission (“SEC”) have warned financial entities that Russia’s invasion of Ukraine will likely result in an elevated number of cyber-attacks and…
Advisor Perspectives Publishes Article by Brian Edelman, FCI CEO & Cybersecurity Expert
- By FCI -
- April 5, 2022 -
Link to: The Top Five Reasons a Security Assessment is Needed for M&A Due Diligence In an Advisor Perspectives guest article, Brian Edelman, FCI CEO & Cybersecurity Expert, details leading reasons for firms to…
FCI Deepens Data Exfiltration Protection for Financial Services Firms
- By FCI -
- March 28, 2022 -
As Regulations and Heightened Cyber Awareness Continue, Zero Trust Alignment is Critical to Avoid Data Exfiltration and Leaks BLOOMFIELD, NJ, March 29, 2022: This past year was a record-breaking year for data breaches. According…
SEC Votes to Propose Rules For Cybersecurity Concerning RIAs
- By John J. Cooney -
- March 9, 2022 -
As discussed in the prior update, the Securities and Exchange Commission (SEC), and specifically the Chair of the SEC, Gary Gensler, emphasized the SEC’s cybersecurity focus during his address at the 2022 Annual Securities Regulation…
Brian Edelman, FCI CEO & Cybersecurity Expert, Presents at CTSR Academy
- By FCI -
- February 10, 2022 -
Brian Edelman joins the Center for Tax, Strategies & Resources (CTSR) Orlando Academy February 9–11, 2022 as an Academy Speaker addressing member attendees who will receive 3-days of curated industry knowledge covering advanced strategies, tools,…
FCI’s Cybersecurity Solutions Create Secure Environments for Financial Services Firms looking to meet the Latest CISA / NYDFS Insight Alerts
- By FCI -
- February 8, 2022 -
With Heightened Geopolitical Conditions, New Warnings Surface to Elevate Cybersecurity BLOOMFIELD, NJ, February 8, 2022: Cybersecurity continues to be a critical business function across industries with high vulnerabilities to threats and those managing sensitive…
SEC Provides More Insight into 2022 Plans
- By John J. Cooney -
- February 5, 2022 -
As discussed in prior updates, the Securities and Exchange Commission (SEC) has increased its efforts with regard to cybersecurity. Towards that end, Chair of the SEC, Gary Gensler, discussed the SEC’s cybersecurity focus during his address at the…
Insurance Town Podcast Interviews Brian Edelman, FCI CEO & Cybersecurity Expert
- By FCI -
- January 25, 2022 -
Brian Edelman joined Insurance Town Podcast host, Heath Shearon, onsite at InsureTech Connect 2021 (ITC) for an insightful conversation about cybersecurity in the insurance industry. Heath, known as the Mayor of Insurance Town,…